Scam-grey milter
Overview
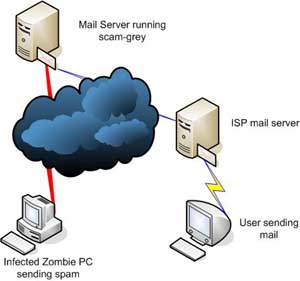
Scam-grey is a milter which filters mail originating from infected zombie PCs. It provides you the ability to mitigate the flow of spam from these computers using greylisting.
Features
Scam-grey milter is simple to configure. It includes features such as:
- Automatic greylisting of botnets
- Greylisting by IP address and CIDR
- Greylisting by ASN
- Greylisting using regular expressions (regex)
- Greylisting hosts without reverse DNS
- Greylisting using DNSBLs
- Whitelisting by IP address and CIDR
- Whitelisting by ASN
- Whitelisting using regular expressions
- Verification of sender address and country
- Automatic detection of small business and home mail servers
- Insertion of ASN header for spam filtering
- POP before SMTP support
- Test mode for evaluation
Performance
Scam-grey milter was designed to be light-weight. It can be used on a mail server with a slow CPU and 128 MB of memory.
How it works
On the first delivery attempt from a PC running Windows, Scam-grey generates a temporary error message. Subsequent delivery attempts made after the delay period will be allowed through. Unlike standard mail servers, virus, trojan infected hosts and zombies are not designed to retry the delivery after a temporary failure.
Scam-grey pairs
- the helo string
- the IP address of the sending server (host)
as a record and returns a temporary failure (SMTP code 450 extended code 4.7.1) if the host is greylisted. The default greylisting delay is eight minutes.
The record is expired if there is no connection for the matching record within the next 24 hours. Click here to see a sample of mail servers which are currently greylisted.
Whitelist
Scam-grey has a configurable whitelist of IP addresses or a range of IP addresses (CIDR). This feature can be used to accept mail from known MS Windows sending servers without any delay.
Hosts with a second level reverse DNS (www.example.com) are not greylisted.
Accept mail from users
Mail from end-users running MS Windows can be accepted without any delay by using any of the following methods:
Users should configure their mail clients (MS Outlook, Eudora, Mozilla Thunderbird) to use the port 587 (MSA) instead of the SMTP port to send mail through the mail server running Scam-grey.
Scam-grey measures the number of hops between the mail server and the computer sending the email. This feature can be used to accept the mail immediately if it falls within five hops.
Scam-grey will accept mail if the connection was authenticated through SMTP AUTH.
Installation
Please read the INSTALL and README files for more information.
Prerequisites
You should have sendmail version 8.12.x or higher installed. Sendmail should
have been built with MILTER support enabled.
You should have the milter library and development kit installed
Download and install P0F ( http://lcamtuf.coredump.cx/p0f.shtml )
Build
1. Extract the scam-grey tarball
2. Change the current directory to the one where the scam-grey source code
was extracted.
3. If you are using FreeBSD, OpenBSD or NetBSD, rename the Makefile.bsd file
to Makefile
If you are using a Linux distribution, rename the Makefile.linux file to Makefile
4. Type make and press Enter to compile scam-grey
Install
1. Copy the scam-grey file created above to the appropriate location
(/usr/local/sbin for example)
2. Generate a new sendmail configuration (sendmail.cf) with the following
additional settings:
define(`confPRIVACY_FLAGS', `needmailhelo')dnl
INPUT_MAIL_FILTER(`scam-grey', `S=unix:/var/spool/scam/scam-grey.sock, F=T, T=S:240s;R:240s;E:5m')dnl
3. Add known external Windows servers to the scam.conf file and copy it to
the /etc/mail directory
4. Create a user (scamgrey for example) which will be used to run the milter
5. Create the /var/spool/scam directory
6. Verify that the user created in step 4 has read-write access to the
/var/spool/scam directory
Using Scam-grey
Startup
1. Login as root and start P0F with the following parameters
p0f -K -U -c 500 -Q /var/spool/scam/p0f.sock -d -q -o /dev/null -u scamgrey 'dst port 25'
A shell script (p0f.sh) is available. You should edit that file before
using it to start p0f.
2. Change the owner of the p0f.sock socket so that it is read-writable by scamgrey
chown scamgrey /var/spool/scam/p0f.sock
3. Start scam-grey milter as a daemon
scam-grey -p unix:/var/spool/scam/scam-grey.sock -u scamgrey -D
4. Restart sendmail if you have generated a new sendmail configuration when
installing scam-grey
Shutdown
Type the following command to stop scam-grey
kill -USR1 `cat /var/spool/scam/scam-grey.pid`
Configuration
Verify whether the default scam.conf file that comes with Scam-grey fits your
site requirements. Review your maillog file regularly and whitelist valid Windows-based mail servers
by adding an entry in the /etc/mail/scam.conf file.
The following syntax is valid when adding entries to bypass greylisting.
WhitelistConnect:192.168.1.5
WhitelistConnect:192.168.0.0/24
WhitelistConnect:/^(mail|list|lyris|smtp|exch|relay)/ie
The regular expression should be in between slashes. Add i at the end
to make the expression case insensitive and e to use extended regex.
More information about the syntax can be found in the regex
documentation.
The following syntax can be used to greylist hosts which
use dynamic IP addresses.
GreylistHost:/^(dhcp|pool)/ie
You can also greylist hosts based on the helo string.
GreylistHelo:/^([0-9]+\.[0-9]+\.)/e
These are the default settings:
GreylistDistance:5
This is the number of hops detected between the remote host and your mail server.
GreylistTime:500
A remote host is greylisted for 500 seconds.
GreylistExpiry:86400
The greylist entries expire after a day.
Greylisting hosts without reverse DNS
Start Scam-grey with the -R switch.
Test mode
If Scam-grey is started with the -t switch, the connection will not be greylisted. A X-Scam-grey: positive header will be inserted to the message instead.
Interaction with antispam filters
Scam-grey inserts a X-Scam-grey: delay 500 seconds header in messages from hosts that have been greylisted. If you are using an antispam filter such as SpamAssassin, you can use the following rule to increase the score for messages sent from Windows hosts or hosts using dynamic IP addresses:
header SCAM_GREY X-Scam-Grey =~ /delay/
score SCAM_GREY 1.0
describe SCAM_GREY Host may be part of a botnet
Greylisting hosts by ASN
Some mail servers block mail from specific countries. Based on the topology of the Internet, it is better to filter by network than by geography. Scam-grey now queries Team Cymru's DNS service to map the IP address of the host to an ASN. You can either greylist
GreylistASN:4134
or whitelist
WhitelistASN:23028
by ASN. You can perform an IP to ASN lookup at http://asn.cymru.com.
The DNS query to find the ASN can be disabled with the following setting:
GreylistFindASN:0
If you are running scam-grey on a high volume mail server, please notify Team Cymru of the amount of queries that may be performed daily.
Greylisting hosts by DNSBL
It is common to use blacklists (DNSBL) for blocking connections. Some backlists may be too aggressive or may cause false positives. You can minimize the impact of these DNSBLs by using them to greylist hosts.
The syntax to query a DNSBL is:
GreylistDNSBL:bl.example.org
where bl.example.org is the zone. You can define several DNSBLs by adding a line for each of them.
License
Copyright © 2004-2010 Eland Systems All Rights Reserved.
- Redistribution and use in source and binary forms must retain the above copyright
notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
- The name of Eland Systems may not be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Download
The download is provided free of charge subject to our license agreement.
Scam-grey source code version 1.6.4 (24 KB)
MD5 50219c21b231db7a95ad2f8574f15250
Previous versions
Scam-grey source code version 1.6.3 (24 KB)
MD5 4a6dd3f36fee56e398c67344463311b0
Scam-grey source code version 1.6.2 (24 KB)
MD5 fac6d7120d19ca69c2b1526728bc5c9e
Scam-grey source code version 1.6.1 (23 KB)
MD5 63baa026ac791c03b974e4704afdf76c
Scam-grey source code version 1.6 (22 KB)
MD5 52fb9b0d1088c924266698cb74c5dfae
Scam-grey source code version 1.5 (22 KB)
MD5 2058bd1923c1d464a6868087ec6e26ea
Scam-grey source code version 1.4 (19 KB)
MD5 851f59103ae2fdda8ce1719f1a75254e
Scam-grey source code version 1.3 (18 KB)
MD5 cc837ed650b2aa7442bfd92f7079abad
Scam-grey source code version 1.2 (18 KB)
MD5 d6f17132126cffb95fd0822cb7016271
Scam-grey source code version 1.1 (18 KB)
MD5 88a09a0405940bdd653577d0d7986dfa
Scam-grey source code version 1.0.1 (15 KB)
MD5 1ccb506cd44723f7d0cc29ac38f91161
Scam-grey source code version 1.0 (15 KB)
MD5 1d88a1b9229ded2ad122ad88225e8998
Contact
Please send your comments and bug reports to scam+grey@elandsys.com.
Credits
P0f - passive OS fingerprinting - Michal Zalewski
We would like to thank Team Cymru for providing an IP to ASN Lookup service.
Scam-grey in action
Mail sent from the following IP addresses are currently greylisted.